The Fraud Triangle’s Achilles Heel – Engineering Trust Through Systematic Controls
in Finance, Accounting and Finance, Cash Flow Improvement, Finance, Financial Leadership, financial planning, Fractional CFO Services, Strategic Planning, All Posts
Outright financial fraud in the form of stealing company funds is something that happens. In the news you can find a variety of examples of systemic cash fraud, and, all too often, this occurs in the accounting and finance areas of the business. Division of duties generically speaking is the root cause in almost all cases.
As mentioned in our previous blog posts on these topics, businesses that single-thread cash movement through the owner are usually insulated but that does not scale. The breakdown can happen when the business reaches a chasm where the financial operations have not expanded with the resources and sophistication to establish appropriate division of duties. In an effort to scale, mistakes are made in standard operating procedures and gaps in cash governance create major risks to the business. In this blog post, we are going to highlight the gaps in specific areas and discuss how we mitigate them.
## **TL;DR:**
Financial fraud exploits predictable gaps in procurement controls:
- Inadequate separation of duties
- Unchecked vendor creation
- Single-person approval authority
- Invisible spending patterns
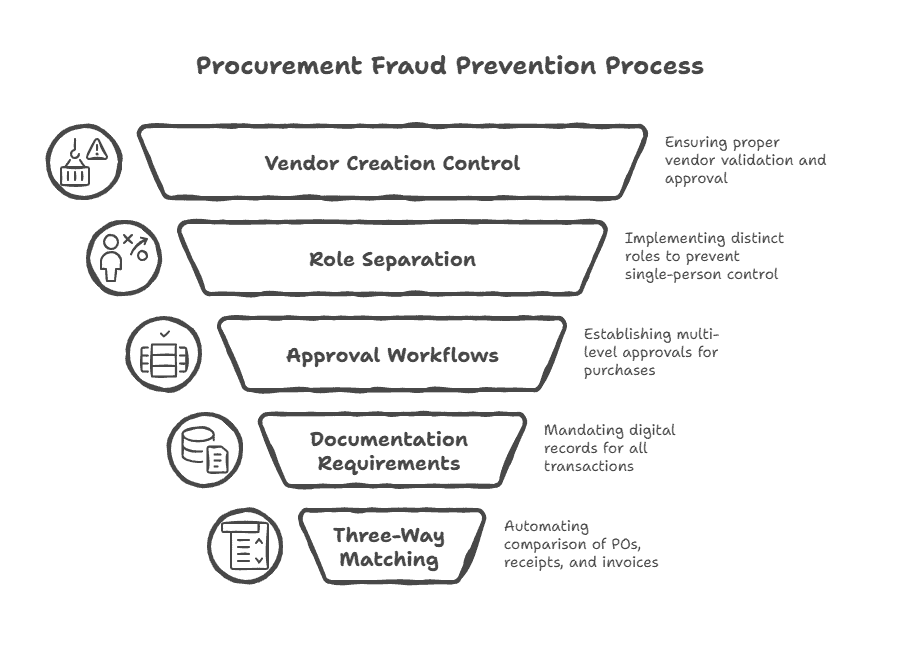
ProcurementExpress systematically closes these vulnerabilities through:
- Enforced role separation
- Multi-level approvals
- Automated three-way matching
- Real-time transparency—making fraud structurally impossible rather than merely detectable
The platform also helps organizations save time and money by automating processes and reducing manual errors.
## **Understanding the Fraud Triangle**
Before we examine specific vulnerabilities, it’s important to understand the fraud triangle—a framework that explains the conditions necessary for fraud to occur. Three elements must align:
- Opportunity: The technical ability to commit fraud without detection.
